I get most excited in these market conditions, whenever I find or rediscover simple ways to earn predictable yields.
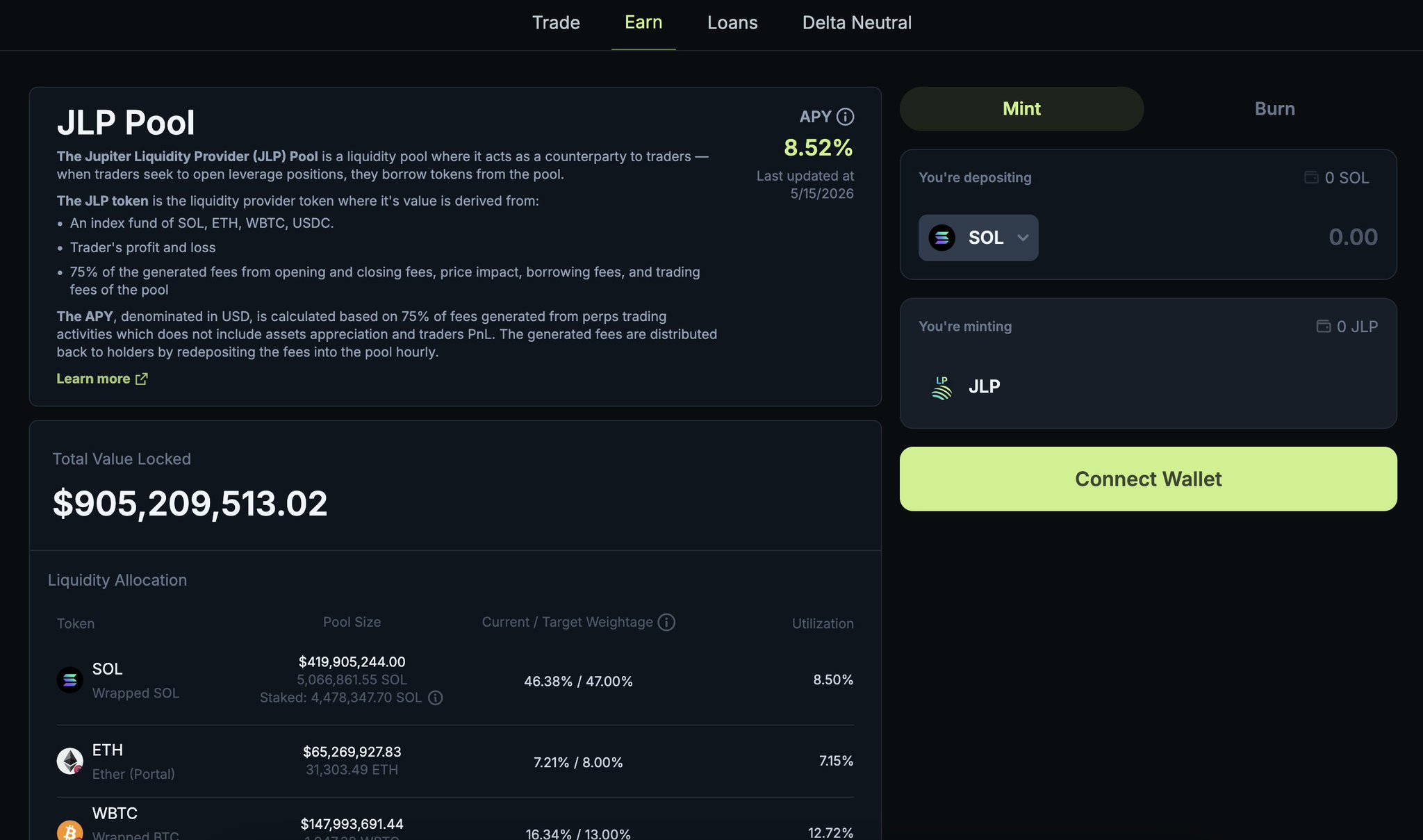
JLP by @JupiterExchange is one tool I think about often.
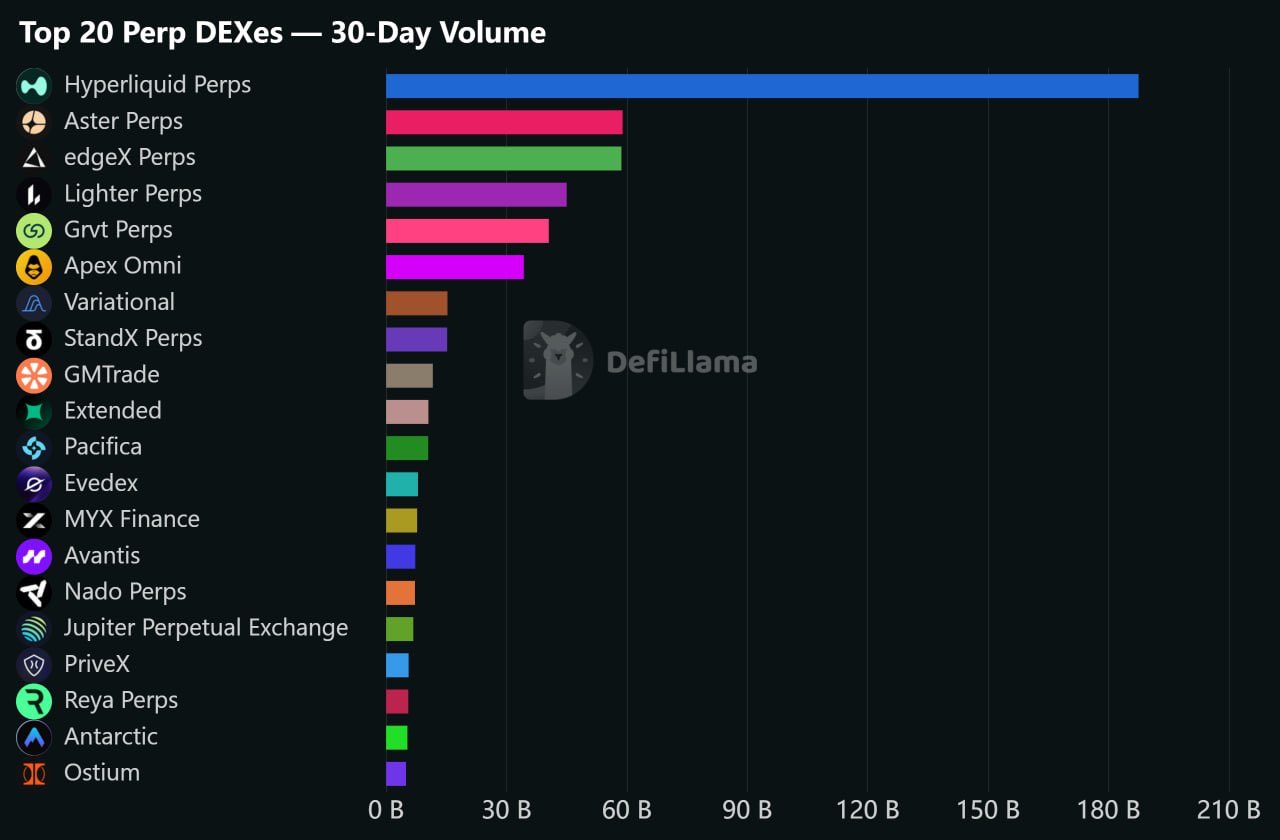
JLP acts as a counterparty to Jupiter traders PnL. Plus, when traders open leverage positions, they borrow tokens from the pool, earning JLP holders more fees.
JLP is 30% stablecoins + 70% (SOL/ETH/BTC).
Meaning, JLP is an index of USDC, SOL, BTC, and ETH so it's not like a stablecoin savings product, more like a less volatile index of these 3 tokens, given 30-32% is stablecoins.
If we look at token performance year-to-date:
BTC = -12%
ETH = -28%
SOL = -32%
JLP = -14.5% 👌
JLP would have been a helluva a buy to protect your holdings start of 2026, and it remains an interesting product even for bull markets, except for you do give up some upside not being more purely exposed to those underlying tokens, assuming they'd be up a lot.
With JLP, we can currently earn 8.52% APY from opening and closing fees, price impact, borrowing fees, and trading fees of the pool. Generated fees are distributed back to JLP holder by redepositing the fees into the pool hourly.
JLP can also be used as collateral with JLP Loans to borrow at 90% LTV, with 95% LLTV on Jupiter, borrowing USDC at 5.99%, with $84M in USDC liq available.
JLP Loans: https://t.co/wQZZurUJQJ
For investors like myself, who are seeking to accumulate these blue chip majors, and get long while markets are down, but also protect against downside while earning fees in the Jupiter trading product suite (perps), JLP feels so damn obvious.
I am overdue to better incorporate JLP into my portfolio.
Learn more about JLP here: https://t.co/lRenvvKmKD